DMI Internship
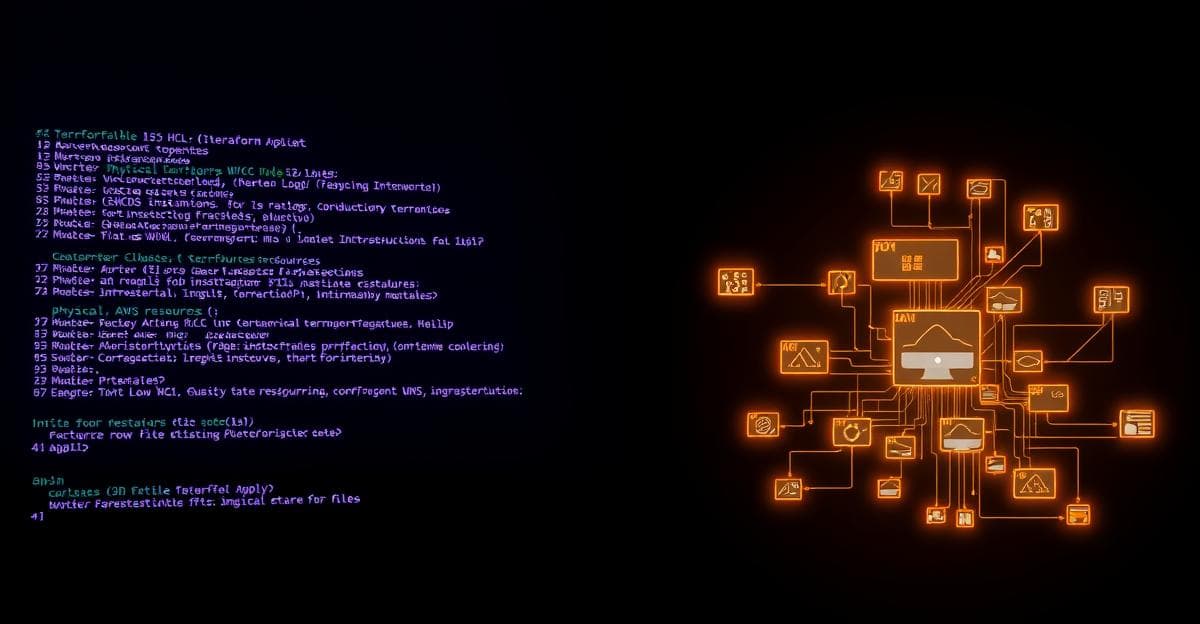
Terraform Infrastructure as Code — AWS Full Stack
Provisioned complete AWS infrastructure from code using Terraform — VPC, subnets, Internet Gateway, Route Tables, Security Groups, EC2, and RDS. Also deployed a static site on S3 + CloudFront using an AI-assisted agentic Terraform pipeline with automated cache invalidation.
Overview
This project covered two distinct Infrastructure as Code (IaC) deliverables using Terraform: full AWS stack provisioning for the 3-tier application, and an agentic AI pipeline for deploying a static website to AWS S3 and CloudFront.
Part 1 — Full AWS Stack via Terraform
Every component of the AWS 3-tier deployment was provisioned entirely from Terraform code — no manual console clicks, no ad hoc resource creation.
Resources Provisioned from Code
- VPC with CIDR block definition
- Public and private subnets across availability zones
- Internet Gateway and Route Tables with correct associations
- Security Groups — tier-specific ingress/egress rules
- EC2 instances — web and application tier with launch configurations
- Amazon RDS MySQL — database instance in private subnet
Engineering Discipline
- All resources tagged consistently for traceability and cost allocation
- Security Group rules defined with minimum required access — no overly permissive CIDR ranges
- State managed cleanly — no manual state manipulation
- Variables used throughout — no hardcoded values in resource definitions
Part 2 — Agentic Terraform Pipeline (S3 + CloudFront)
The static website deployment used an AI-assisted agentic pipeline built with Claude Code, automating the full Terraform workflow:
scaffold-terraform → tf-validate → tf-plan → tf-apply → deploy → cf-invalidate
Each stage was executed by a specialised agent step, with CloudFront cache invalidation triggered automatically on successful deployment — ensuring the live site always serves the latest content without manual intervention.
Technologies Used
- Terraform — Infrastructure as Code throughout
- AWS S3 — static website hosting with bucket policy
- AWS CloudFront — CDN with Origin Access Control (OAC)
- Claude Code / MCP — agentic pipeline orchestration
- HTTPS enforcement — CloudFront configured to redirect HTTP to HTTPS
Results
Complete AWS infrastructure provisioned from code in a single terraform apply. Static site live on CloudFront with HTTPS enforced and automatic cache invalidation on deploy. Zero manual AWS Console interaction required after initial credential configuration.
Key Learnings
Infrastructure as Code is not just about automation — it is about auditability. When every resource is defined in code, every change is a commit, every configuration decision is reviewable, and every deployment is reproducible. The agentic pipeline extension demonstrated that IaC and AI-assisted workflows are not alternatives; they compound each other's value.